Google Just Slashed the Quantum Deadline for Cracking Crypto — Here is How to Protect Your Wallet Before 2032
Think of your Bitcoin private key like a bank vault combination. Until yesterday, experts said a quantum computer would need roughly 10 million qubits — the quantum equivalent of processing power — to crack it. That felt safe. Like saying you need a nuclear reactor to rob a bank. Distant. Theoretical.
Google just blew that timeline apart.
On Monday, Google’s Quantum AI team dropped a research paper that should make every crypto holder sit up straight. Their new estimate: fewer than 500,000 physical qubits could break the elliptic curve cryptography protecting Bitcoin and Ethereum. That is a 20-fold reduction from prior estimates. And they think a quantum computer could derive your Bitcoin private key in as little as nine minutes.
Nine minutes. That is shorter than most Bitcoin transactions take to confirm.
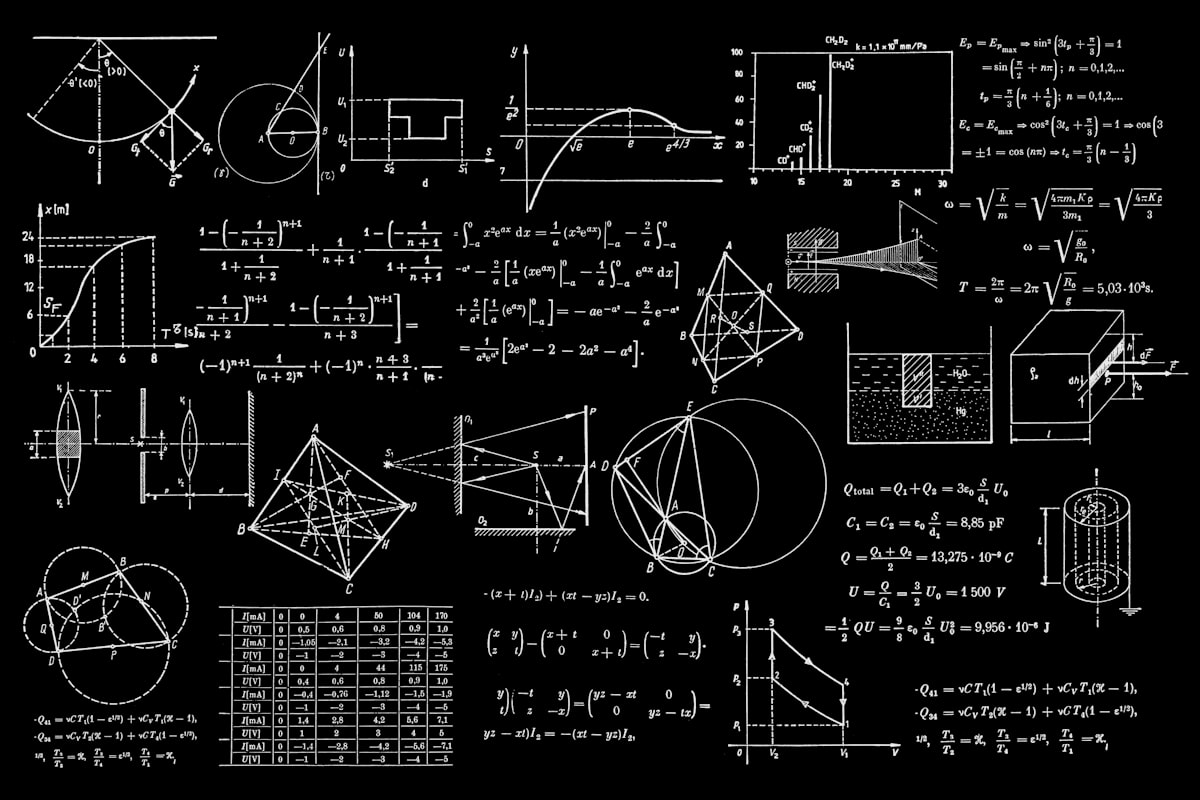
What Google Actually Found
Here is the meat of it. Google compiled two quantum circuits designed to break ECDLP-256 — the cryptographic math behind virtually every major blockchain. The results were not hypothetical hand-waving. They ran actual tests on a superconducting-qubit cryptographically relevant quantum computer (CRQC).
Their conclusion: a quantum attacker could perform what is called an “on-spend attack” — deriving a private key from a public key the moment it is broadcast during a transaction — within Bitcoin’s 10-minute block window. In fact, they estimated roughly 9 to 12 minutes to crack a key from an exposed public key.
But here is the thing that should really scare Ethereum holders.
Ethereum Has a Bigger Problem Than Bitcoin
Bitcoin’s UTXO model means public keys are only exposed during transactions. If you never reuse addresses, your key stays hidden until you spend. Ethereum does not work that way.
The moment an Ethereum account sends its first transaction, its public key is permanently visible on the blockchain. Forever. No amount of careful behavior fixes this — it is baked into Ethereum’s account model.
Google’s researchers called this an “at-rest attack” vulnerability. A quantum attacker does not need to race the clock. They can take their sweet time. And the numbers are staggering: Google estimated that the 1,000 wealthiest exposed Ethereum accounts — holding roughly 20.5 million ETH — could be cracked in fewer than nine days.
Let that sink in. Nine days to drain the top 1,000 accounts on Ethereum.
The Q-Day Clock Just Sped Up
Ethereum researcher Justin Drake, who co-authored the paper, said his confidence in “Q-Day” arriving by 2032 has “shot up significantly.” He puts the probability at at least 10% that by 2032, a quantum computer could recover a private key from an exposed public key.
Ten percent might not sound like much. But consider this: if someone told you there was a 10% chance your house would burn down in the next six years, you would buy insurance tomorrow.
Google itself set a 2029 deadline for its own post-quantum cryptography migration — just three years away. Crypto entrepreneur Nic Carter called elliptic curve cryptography “on the brink of obsolescence.” The vibes are shifting fast.
What You Can Do Right Now
This is not a “sit back and watch” situation. Here are concrete steps you can take today:
1. Stop reusing Bitcoin addresses — immediately. Every time you spend from an address, you expose its public key. If you are reusing addresses, you are handing quantum attackers a gift. Use a fresh address for every transaction. Most modern wallets do this by default, but double-check yours.
2. Check your Ethereum exposure. If you have ever sent a transaction from your Ethereum wallet, your public key is permanently exposed. There is nothing you can do about it right now except wait for protocol-level fixes. But at least know your risk.
3. Move long-term holdings to cold wallets that have never broadcast. The safest Bitcoin is Bitcoin sitting in an address whose public key has never been revealed. If you have a “set and forget” wallet from 2017 that has never spent, your funds are quantum-safe for now.
4. Start paying attention to post-quantum cryptography (PQC) upgrades. Ethereum has already released a post-quantum roadmap. Vitalik Buterin has proposed four specific fixes: validator signatures, data storage, accounts, and proofs. Bitcoin developers, according to Nic Carter, have a “worst in class approach” so far. That needs to change.
5. Diversify into chains already working on quantum resistance. Some newer protocols are being designed with PQC from the ground up. If you are allocating new capital, factor quantum readiness into your thesis.
The Uncomfortable Truth
Most crypto holders are ignoring this. The market is not pricing it in. Bitcoin did not crash on this news. Nobody is panic-selling. And that is exactly the problem.
Quantum computing risk is the kind of threat that feels imaginary until it is not. It is like climate change for your portfolio — slow, compounding, and devastating when it arrives. The difference is that with climate, you get gradual warnings. With quantum, the moment someone cracks a live private key, the game is over. There is no “partial breach.”
Google did not publish this paper to scare people. They published it because they believe the timeline is compressing faster than anyone expected, and the crypto community needs to start migrating now — not in 2030, not when a quantum computer actually exists at scale, but today.
In my view, the smart play is simple: protect what you can protect now, watch the PQC developments closely, and do not assume the 10-year timeline is actually 10 years. Google just told us it might be six.
Sources: Cointelegraph | Google Research | Cointelegraph – 2029 Deadline