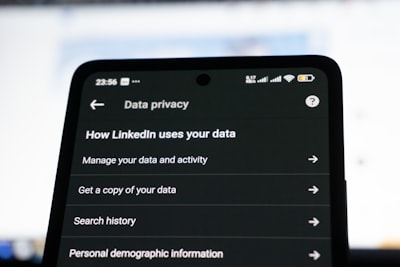
Does the White House App Track You? What Network Traffic Analysis Reveals in 2026
Does the White House app track its users? A cybersecurity team just answered that question by intercepting every single packet the official iOS app sends home — and what they found should concern anyone who’s ever installed it.
The answer isn’t a simple yes or no. It’s worse. It’s complicated enough that most people won’t understand the implications.
White House App Network Traffic: The 77% Problem
Researchers at Atomic Computer set up a man-in-the-middle proxy on an iPhone and browsed every tab in the White House app (v47.0.4). They intercepted 206 total requests.
Here’s the number that matters: only 48 of those requests — 23% — went to whitehouse.gov. The other 158 requests (77%) went to third-party services including Elfsight, OneSignal, YouTube, Google DoubleClick, Facebook, and Twitter.
Think about that ratio. For every one request fetching actual government content, roughly three requests fly out to ad networks, analytics platforms, and social media CDNs. This isn’t a government app. It’s a tracking apparatus with a government skin.
What OneSignal Knows About You
The most damning finding involves OneSignal, a push notification and analytics service. On every app launch, the app sends a PATCH request to api.onesignal.com containing:
- Your IP address (full IPv6 or IPv4)
- Device model and OS version (fingerprint)
- Timezone and country (geographic narrowing)
- Exact timestamps for first and last activity
- Session duration in seconds
- How many times you’ve opened the app
- WiFi vs. cellular connection type
- Whether your device is jailbroken
- A persistent unique identifier tracking you across sessions
OneSignal doesn’t just log your current session. It maintains a persistent profile. When the researchers launched the app from a different network, OneSignal logged the new IP address against the same unique ID from the previous session. They’re building a longitudinal map of your movements and device usage.
The Elfsight Problem: 13 Domains, One Widget Provider
The app connects to 13 different Elfsight domains. Why does that matter? Because Elfsight uses what’s called a two-stage JavaScript loader. The app sends widget IDs to core.service.elfsight.com, and the server responds with JavaScript files to inject and execute.
This is a supply chain risk. The server decides what code runs in your app session. If Elfsight’s infrastructure were compromised — or if they simply decided to inject tracking scripts — the White House app would execute them without any approval process.

Google DoubleClick Tracking Inside a Government App
The YouTube embeds in the app load Google’s advertising infrastructure. Requests to googleads.g.doubleclick.net and static.doubleclick.net confirm that Google’s ad tracking fires inside what users reasonably assume is a government-secure environment.
Facebook CDN images load from fbcnd.net servers. Twitter/X images load from pbs.twimg.com. Each of these connections is an additional data-sharing pathway the user never explicitly consented to.
Is This Normal for Government Apps?
No. Most serious government apps minimize third-party dependencies specifically because of the tracking and security risks involved. The UK’s NHS app, for example, limits telemetry. The Finnish government’s apps are built with privacy-by-design principles.
The White House app, by contrast, embeds six social media widgets (TikTok, Instagram, Facebook, YouTube, X, and Truth Social), each with its own set of third-party dependencies. The social media integrations aren’t just displaying content — they’re executing tracking scripts and setting cookies on every visit.
What You Can Do Right Now
If you have the White House app installed, consider these steps:
- Uninstall it. The website provides the same content without the tracking overhead.
- Use a mobile browser with tracking protection. Firefox Focus or Brave will block most of these third-party requests.
- Review your app permissions. Check what other government or news apps have access to on your device.
- Use a VPN. While OneSignal still tracks device info, a VPN masks your actual IP address from their longitudinal profile.
The bottom line: the White House app treats user privacy the way most consumer apps do. That might be acceptable for a shopping app. For an official government application, it’s a failure of stewardship.
Sources: Atomic Computer | Hacker News Discussion | Previous Static Analysis